Information Security You Can Trust
DealRoom | Secure Project Management Software for M&A
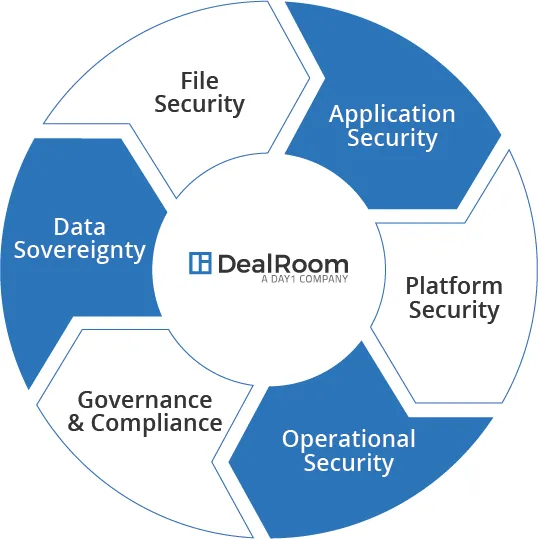
Dealroom not only meets industry security standards, but goes the extra mile to ensure all information is kept secure and documents are protected. Our platform’s security measures provide clients with controls, reporting, and procedures required to keep all their data and operations safe. We go above and beyond industry standards to reduce risk and eliminate security fears.
Secure Virtual Data Room to Meet Your Needs

View-only access allows for viewing, but does not give access to downloading documents. You no longer have to worry about documents being saved for later.

Restrict the portion of an individual document viewable by a particular group or individual. This can facilitate collaboration, safely.

Maintain complete control over who can access specific information in your data room due diligence. Keep proprietary information out of the wrong hands.
Decide what documents need a watermark with the click of a button.
Easily add users and set their access permissions to exactly what you want.
Our monitoring and reporting lets you gain insight on user’s login time, files accessed, and time spent with docs.
Confidential Application and File Storage
Strict single-user ID and password protocols protect all your data. Each user has their own unique login.
Multi-factor password authentication reduces the risk of password theft. It requires users and administrations to login with two factors.
All data is encrypted and protected in transit and at rest. This prevents unauthorized data visibility.
Users can personalize allowances for access and permissions. Admin teams can also set controls across all users.
Data can be stored in private cloud servers. This allows for data to be stored and accessed by the appropriate parties.
Eliminate the use of insecure email to share and transfer sensitive documents. Keep all communication within the secure platform.
Secure File Sharing and Data Storage Platform
All data is supported by 256-bit AES data encryption, so it is safe and secure.
Comprehensive audit reports and analytics for regulated and non-regulated industries.
Disaster recovery with repeated failover capabilities and data center recovery testing.
Compliance with data privacy laws enabled by distributed content node architecture.
Extension of existing enterprise security technologies to maximize ROI.
Global storage network to enable compliance with regional data sovereignty requirements.
Complete M&A Project Management Application Control
Configurable control of file, folder and workspace access by group, user and device.
Team resource management facilitated by assignable roles.
Full audit trails with real-time status and detailed compliance reports.
Control of specific application functionality, such as local file sync and mobile device access.
Our software includes a risk-based multifactor rules engine to ensure hazard avoidance.
As part of our security promise to our clients, DealRoom has specific data-driven authentication rules.
File Backups & Redundancy
All our servers and customer data are automatically backed up daily. If hardware failure or an AWS outage should occur, all customer data can be fully recovered.
Secure Operation and File Maintenance
System performance and information security is continuously monitored by our team of highly skilled engineers. This ensures that all incidents will be handled in a timely manner by trained personnel and properly documented.
Dealroom’s security team closely monitors any updates, alerts, and advisories regarding security from system vendors, software vendors, security organizations and authorities. Our security team then follows through with appropriate mitigation methods and security controls.
